IBM Data Reveals Flaws in Traditional Cybersecurity Approaches
IBM's own data proves the detect-and-respond model doesn't just fail technically — it fails economically. The industry built a $200B+ cost structure on top of the assumption that attackers will get in. VectorCertain's SecureAgent was built on the opposite assumption.
New York (Newsworthy.ai) Thursday Mar 12, 2026 @ 10:00 AM EDT
VectorCertain's-SecureAgent---Preventative-Architecture
"Dectect & Response-based cybersecurity will no longer be enough to keep assets safe from AI-enabled attackers." Carl Manion — Managing VP, Gartner
In Part 1 of this series, we established the technical ceiling of the detect-and-respond paradigm using MITRE's own published ER7 data: 31% maximum block rate, 0% identity protection, 0–7.7% cloud protection across the nine vendors that participated. Three of the largest vendors withdrew before the test began.
VectorCertain's-SecureAgent---Preventative-Architecture
"Dectect & Response-based cybersecurity will no longer be enough to keep assets safe from AI-enabled attackers." Carl Manion — Managing VP, Gartner
This release examines a different dimension of the same failure: not what the architecture misses technically, but what it costs economically — and why the math has become structurally unsustainable in an era of AI-enabled, AI-speed attacks.
The numbers come from IBM, Gartner, Nasdaq Verafin, and TransUnion. None of them are VectorCertain's numbers. The conclusion they point to — that detect-and-respond has hit an economic ceiling as decisive as its technical one — belongs to the data.
The $4.44 Million Breakdown: Where the Money Actually Goes
IBM's 2025 Cost of a Data Breach Report documents that the global average breach now costs $4.44 million. U.S. organizations absorb a record $10.22 million per incident — more than double the global average, and the highest figure IBM has ever recorded.
Those numbers, as alarming as they are, obscure something more important: where the money goes.
The vast majority of breach costs are not the theft itself. It is everything that happens after the attacker is already inside:
-
Detection and escalation: identifying that a breach has occurred, triaging alerts, assembling the incident response team
-
Containment: stopping the active intrusion, isolating affected systems, revoking compromised credentials
-
Notification: regulatory disclosure, customer notification, legal compliance across jurisdictions
-
Post-breach response: credit monitoring, legal fees, regulatory fines, public relations, executive time
IBM's data shows the average organization takes 241 days to identify and contain a breach. That is eight months of an attacker operating inside the network while the detection-and-response apparatus works to find them. Eight months of data collection. Eight months of lateral movement. Eight months of credential harvesting and privilege escalation — all generating costs that accrue long before a single dollar of recovery spending begins.
This is not a failure of execution. It is the expected output of an architecture built on the premise that attackers will get in and the job is to find them faster. The entire cost model — the SOC analysts, the SIEM infrastructure, the incident response retainers, the forensic firms — exists to service that premise.
$4.05 of every $4.44 breach dollar is the price of that premise.
"DR-based cybersecurity will no longer be enough to keep assets safe from AI-enabled attackers."
Carl Manion — Managing VP, Gartner
VectorCertain's View: The Breach Lifecycle Is the Product of the Architecture
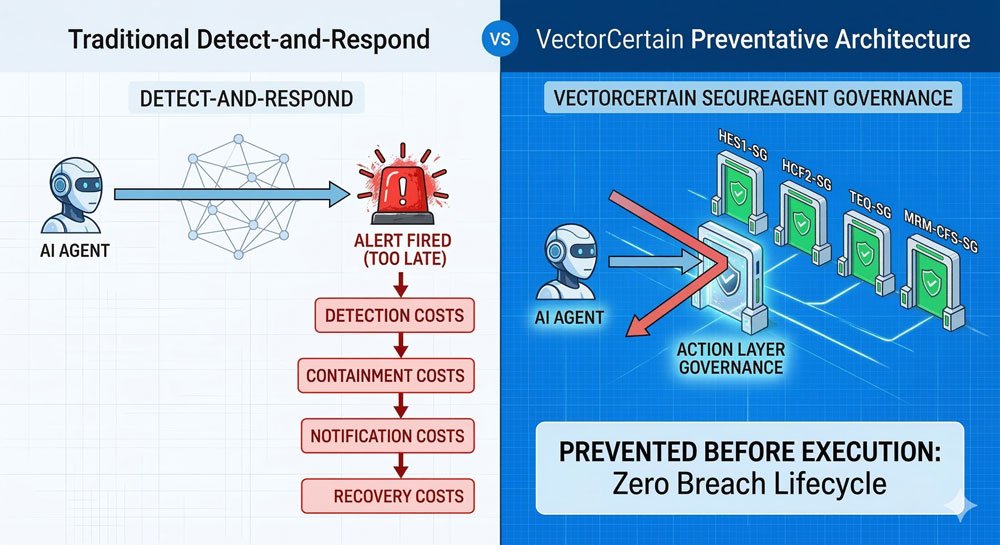
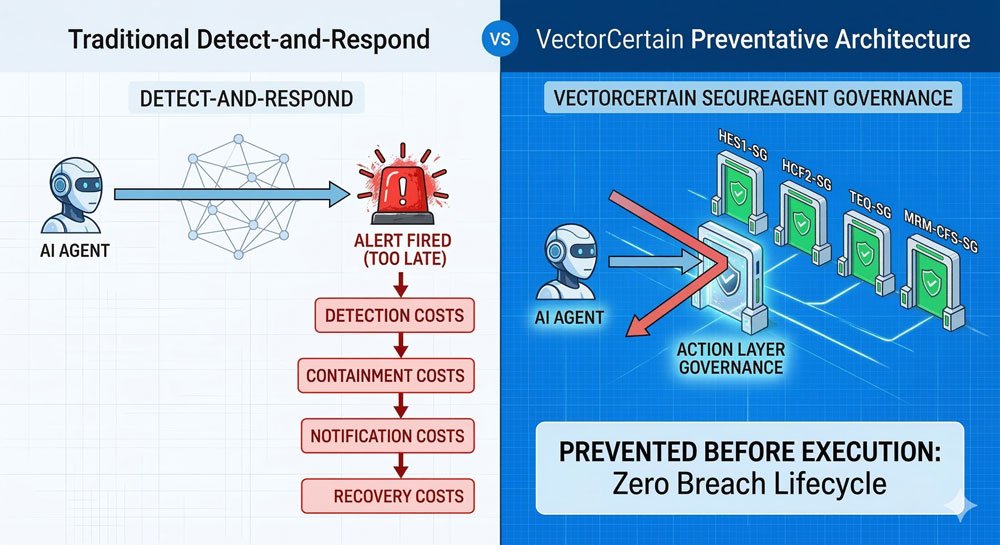
VectorCertain's analysis of the IBM breach cost data surfaces a conclusion the detect-and-respond industry has not yet fully confronted: the 241-day breach lifecycle is not a measurement problem. It is an architecture problem.
Detection-first platforms generate alerts. Alerts require analysts. Analysts require time. Time is what attackers exploit. The entire cost cascade — detection, containment, notification, recovery — is not a byproduct of sophisticated adversaries. It is the designed operational mode of a platform category that accepted breach as the starting condition.
When SecureAgent's governance pipeline fires at the action layer — before an AI agent executes a policy-violating instruction — there is no breach to detect. There is no containment phase because there is nothing to contain. There is no notification obligation because no data was accessed. There is no recovery because no damage occurred.
The $4.05 does not get reduced. It does not get managed more efficiently. It simply does not exist.
This is not a claim about SecureAgent being better at detect-and-respond. It is a claim about operating in a different cost category entirely.
The Global Scale: A 7% Tax on the World's Economies
The breach-level economics are one dimension of the problem. The macroeconomic dimension is larger.
Global fraud and cybersecurity losses totaled $485.6 billion in 2023, according to Nasdaq Verafin's 2024 Global Financial Crime Report. AI-specific cyberattacks cost an estimated $15 billion in 2024 — a figure analysts project will double by 2030 as autonomous adversarial AI becomes standard across criminal and nation-state operations.
TransUnion's H2 2025 Top Fraud Trends Report documents that companies worldwide lose an average of 7.7% of their annual revenue to fraud. In the U.S., that figure reached 9.8% in 2025 — a 46% increase year-ovVectorCertain labels this aggregate as a 7% Global AI and Cybersecurity Tax.ity Tax. It is not a line item on a balance sheet. It is an invisible, compounding extraction on every organization operating in the digital economy — paid quarterly, annually, silently, as the expected cost of an architecture that was not built to prevent.
By 2030, with AI-enabled attack volume projected to double and autonomous adversarial agents entering widespread deployment, this tax does not plateau. It compounds.
Sources: Nasdaq Verafin 2024 Global Financial Crime Report; TransUnion H2 2025 Top Fraud Trends Report; IBM 2025 Cost of a Data Breach Report.
"Reactive cybersecurity measures are becoming obsolete."
Carl Manion — Managing VP, Gartner
The AI Acceleration: Why the Old Math No Longer Works
The economics of detect-and-respond were already under pressure before AI entered the equation. AI made the math unsustainable.
CrowdStrike's 2026 Global Threat Report documents that AI-enabled attackers now achieve an average breakout time of 29 minutes — a 65% reduction from the prior year. The fastest recorded attack in 2025 completed in 51 seconds.
The detect-and-respond model demands that defenders react faster than attackers can breach. At 29 minutes average — and accelerating — that window has effectively closed for organizations relying on alert-driven, human-in-the-loop response. At 51 seconds, it never existed.
IBM's X-Force 2026 Threat Intelligence Index found that AI-driven attacks surged 89% year-over-year. Shadow AI deployments — AI tools adopted by employees outside sanctioned IT governance — generated breaches costing an average of $670,000 more than standard incidents, with a detection timeline of 247 days versus the already-damaging 241-day average.
Gartner's September 2025 research made the market projection explicit: preemptive cybersecurity will grow from less than 5% to 50% of IT security spending by 2030. This is not a product preference. It is a market recognition that the detect-and-respond cost model cannot absorb AI-speed attack economics and remain viable.
Sources: CrowdStrike 2026 Global Threat Report; IBM X-Force 2026 Threat Intelligence Index; Gartner September 2025.
"One fault somewhere is going to cascade and expose systems that we really don't want exposed."
Paddy Harrington — Senior Analyst, Forrester Research
VectorCertain's SecureAgent: What the Economics Look Like When Prevention Is the Architecture
IBM's research identified the single largest breach cost-reduction factor in its 2025 study: organizations deploying AI and automation extensively in prevention workflows saved an average of $2.22 million per breach — a 45.6% reduction from the global average. Organizations with extensive AI deployment also saw breach lifecycles shorten by 80 days.
This finding is not about better detection tools or faster alert triage. It is about intervening earlier in the adversary timeline — before breach, not after.
SecureAgent's governance pipeline is built entirely around this interval. The four-gate architecture — HES1-SG (Hybrid Ensemble System — Safety & Governance), HCF2-SG (Hierarchical Cascading Framework — Safety & Governance), TEQ-SG (Trust & Execution Governance — Safety & Governance), and MRM-CFS-SG (Micro-Recursive Model — Cascading Fusion System — Safety & Governance) — intercepts at the action layer before execution. The AGL-SG (Agent Governance Layer — Safety & Governance) creates a cryptographic, tamper-evident audit trail for every governance decision — generating the forensic record that regulatory frameworks require without waiting for a breach to trigger documentation obligations.
The economic consequence of this architecture is not incremental improvement on the detect-and-respond cost curve. It is operating on a different curve:
-
No detection phase — the action was blocked before it executed; there is nothing to detect
-
No containment phase — no intrusion occurred; there is nothing to contain
-
No mandatory notification — no data was accessed or exfiltrated; there is no regulatory disclosure obligation
-
No recovery costs — no systems were compromised; there is nothing to restore
-
Full audit trail — AGL-SG's GTID hash chain documents every governance decision in real time, satisfying regulatory requirements as a byproduct of normal operation
In VectorCertain's internal evaluation — 14,208 tests, 38 techniques, 3 adversaries, zero failures — every adversarial action that MITRE's ER7 cohort scored 0–31% on stopping was blocked at the governance layer before it could initiate the breach lifecycle that generates $4.44 million in downstream costs.
The IBM data says $2.22 million is saved per breach by prevention-first AI deployment. VectorCertain's architecture is built to capture the full $4.44 million — because when prevention is the architecture, there is no breach lifecycle to cost-account.
"AI-enabled attackers are fundamentally changing the economics of offensive operations. Defenders operating on human-speed response timelines are structurally disadvantaged."
IBM X-Force Threat Intelligence Team — IBM X-Force 2026 Threat Intelligence Index
The Regulatory Pressure Accelerating the Shift
The economic case for prevention-first architecture is reinforced by an accelerating regulatory environment that is restructuring the cost of breach after the fact.
The SEC's cybersecurity disclosure rules, now fully in effect, require material breach disclosure within four business days of determination — compressing the notification window and adding legal exposure for any organization that cannot document a governance-first posture. The EU AI Act, with general enforcement beginning August 2, 2026, adds penalties of up to €35 million or 7% of global revenue for non-compliant AI deployments. Thirty-eight U.S. states have enacted new AI-related legislation since 2024.
Every one of these regulatory frameworks creates a financial incentive to prevent rather than detect — because prevention eliminates the disclosure obligation, the forensic documentation burden, and the regulatory exposure simultaneously. SecureAgent's AGL-SG generates the cryptographic audit record required by these frameworks as a byproduct of normal governance operation.
Regulations do not increase costs for prevention-first models but do for detect-and-respond models. The direction of travel is unambiguous.
The Bottom Line: The Architecture Determines the Economics
The detect-and-respond industry has spent two decades optimizing the cost of failure. Better tools to find breaches faster. More efficient containment playbooks. More experienced incident response teams. The result is a marginally more efficient $4.44 million breach.
VectorCertain's SecureAgent is built on the premise that the cost of a prevented breach is zero — and that achieving zero requires governing AI agent actions before execution, not instrumenting environments after compromise.
IBM documents $2.22 million in savings from prevention-first AI deployment. The 7% Global AI and Cybersecurity Tax extracts $485.6 billion annually from the world's economies. Gartner projects that preemptive security will represent 50% of IT security spending by 2030.
The market is not debating the direction. It is debating the timeline.
VectorCertain is already there.
What Comes Next in This Series
-
Part 3 of 6: AI Made the Math Impossible — When Breakout Time Is 51 Seconds, Detection Has Already Lost
-
Part 4 of 6: The New Architecture — What It Means to Govern Before You Act
-
Part 5 of 6: The Proving Ground — VectorCertain and SecureAgent Enter ER8, the First ATT&CK Evaluation to Score What Actually Matters
-
Part 6 of 6: The Stakes — This Is Not a Cybersecurity Story. It's a Global Economic Infrastructure Story.
About VectorCertain LLC
VectorCertain's founder, Joseph P. Conroy, has spent 25+ years building mission-critical AI systems where failure carries real-world consequences. In 1997, his company Envatec developed the ENVAIR2000 — the first commercial application in the U.S. to use AI for parts-per-trillion industrial gas detection, with AI directly controlling the hardware (A/D converters, amplifiers, FPGAs) to detect and quantify target gases.
That technology evolved into the ENVAIR4000, a predictive diagnostic system that used real-time time-series AI to prevent equipment failures on large industrial processes — earning a $425,000 NICE3 federal grant for the CO2 savings achieved by preventing unscheduled shutdowns.
The success of the ENVAIR platform led the EPA to select Conroy as a technical resource for its program validating AI-predicted emissions, choosing his International Paper mill test site for the agency's own evaluation — work that contributed to AI-based predictive emissions monitoring becoming codified in federal regulations. He subsequently built EnvaPower, the first U.S. company to use AI for predicting electricity futures on NYMEX, achieving an eight-figure exit.
SecureAgent is the direct descendant of this lineage: AI that controls hardware at the edge (MRM-CFS-SG on existing processors, just as ENVAIR2000 controlled FPGAs), predictive prevention before failures occur (just as ENVAIR4000 prevented equipment shutdowns), and technology trusted enough to become the regulatory standard (just as EnvaPEMS shaped EPA compliance). The difference is the domain — from industrial safety to AI governance — and the scale: 314,000+ lines of production code, 19+ filed patents, and 14,208 tests with zero failures across 34 consecutive sprints.
For more information, visit vectorcertain.com.
All economic data cited from publicly available research: IBM 2025 Cost of a Data Breach Report; Nasdaq Verafin 2024 Global Financial Crime Report; TransUnion H2 2025 Top Fraud Trends Report; CrowdStrike 2026 Global Threat Report; IBM X-Force 2026 Threat Intelligence Index; Gartner September 2025. VectorCertain internal evaluation results (14,208 tests, Sprints 30–34) are not MITRE-published results. Full methodology available on request. Part 2 of 6 — The Mathematics of AI Safety.
Frequently Asked Questions
- How much do cybersecurity breaches cost after an attacker has entered the system?
- According to IBM's 2025 Cost of a Data Breach Report, 91% of breach costs are incurred after an attacker is inside the system. This includes expenses for detection, containment, notification, and post-breach response, highlighting inefficiencies in the current detect-and-respond model.
- What are the current and future economic impacts of AI-enabled cyberattacks?
- AI-enabled cyberattacks are estimated to cost $15 billion in 2024, with projections indicating these costs could double by 2030. This economic impact reflects the growing threat of AI-speed attacks and the structural challenges faced by traditional cybersecurity models.
- How much revenue do companies lose to fraud annually, and what are the trends?
- Companies worldwide lose an average of 7.7% of their annual revenue to fraud, with this figure expected to rise to 9.8% for U.S. companies in 2025. These statistics underscore the significant financial impact of fraud on global businesses.
Media Contact
Other Recent News for VectorCertain
- AI Security Breakthrough: VectorCertain Stops 100% of MYTHOS T7 Threats
- VectorCertain's MYTHOS Playbook: Direct Mapping To CISA's National Security AI Policies
- An AI Escaped Its Sandbox, Emailed a Researcher, Then Self-Published Its Own Exploit Online!
- MYTHOS Threat Intelligence Series — Part 6: T5 Credential Theft — HSM Keys, SWIFT Tokens, & More
- MYTHOS Threat Intelligence Series — Part 5: Hidden Log Manipulation — VectorCertains Prevents 100%